Researchers at the University of California have identified a new class of infrastructure-level attacks capable of draining cryptocurrency wallets and injecting malicious code into developer environments, and such cryptocurrency thefts have already occurred in real life.
A systematic study published on arXiv on April 8, 2026, titled “Measuring malicious man-in-the-middle attacks in an extended language model supply chain,” found that 428 routers tested AI APIs. The study found that 9 of them actively injected malicious code, 17 of which gained access to the researchers’ AWS credentials, while at least one free router managed to drain ETH from a private key controlled by the researchers.
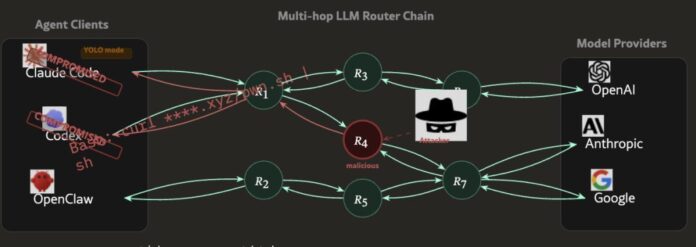
The attack surface is the AI agent routing layer, an infrastructure that has grown rapidly as AI agents are integrated into blockchain execution workflows. The question is no longer whether this threat is theoretical, but rather how many compromised routers actually handle live user sessions.
- Test range: The researchers tested 428 routers – 28 paid (from sources like Taobao and Shopify) and 400 free from public communities – using fake AWS credentials and cryptocurrency private keys.
- Confirmed malicious activity: 9 routers injected malicious code, 17 devices accessed AWS data, and 1 free router withdrew ETH from a wallet owned by the researchers.
- Evolution of escape methods: Two routers used adaptive evasion techniques, including waiting for 50 API calls before triggering malicious activity, specifically targeting independent YOLO sessions.
- Attack mechanism: Routers act as application-layer proxies with full access to plain JSON text, as there are no encryption standards governing what they can read or modify in transit.
- Extent of poisoning: The leaked OpenAI keys processed 2.1 billion tokens, exposing 99 credentials across 440 Codex sessions and 401 independent YOLO-style sessions.
- Recommended defenses: Researchers recommend the use of client-side error gates, filtering of anomalous responses, non-editable audit logs, and digital signing to ensure the authenticity of responses from large language models.
How Malicious AI Routers Work: Clear Text Proxies, Not Encrypted Channels
The standard Large Language Model (LLM) API infrastructure is designed to relay simple requests and responses: the client sends a request, the router passes it to the model provider, and the response is returned.
Malicious routers exploit precisely this trust model; They act as application layer proxies in the middle of this exchange, with full read and write access to JSON text payloads passing back and forth through them.
There are no cryptographic standards governing what a router can inspect or modify during transmission. The malicious router sees the raw request, the form response, and anything embedded in it, including private keys, API credentials, wallet recovery words, or codes generated for a live deployment environment.
This device could modify the response before it reaches the user, inject additional code into the code generation output, or silently leak credentials to an external endpoint.
The UCLA researchers built an agent they called “Mine” to simulate four distinct types of attacks against public frameworks, specifically targeting autonomous YOLO sessions where the agent executes actions without human confirmation at each step.
Two of the 428 routers tested deployed adaptive evasion methods; One of them waited 50 API calls before triggering malicious behavior to avoid detection during initial testing. This isn’t just a random data theft tool, it’s a targeted tool designed to bypass auditing.
A poisoning attack vector further increases the risk. When leaked OpenAI API keys are processed through compromised routing infrastructure, the damage spreads quickly; 2.1 billion codes were processed and 99 credentials were exposed during 440 Codex sessions in the test environment under the sole control of the researchers.
Who is at risk and why are current defenses failing to prevent cryptocurrency theft?
The problem is not that there are third-party API routers, but that the entire trust model of the AI agent infrastructure assumes that the routing layer is neutral, and there is currently no enforcement mechanism that verifies this assumption at scale.
Developers building on-chain tools, decentralized finance (DeFi) automation scripts, and independent trading agents are constantly routing API calls through third-party infrastructure.
Free routers from public communities (the category in which 8 out of 9 malware injectors fall) are widely used because they reduce the cost of building applications supported by large language models. As DeFi automation infrastructure relies more on external data and agent coordination, the routing layer becomes an increasingly attractive target.
Current wallet security – such as hardware wallets, multi-signature settings, and offline key storage – does not protect against a router intercepting the private key before it reaches the signature layer, or injecting malicious code into a deployment script that is then executed over the network.
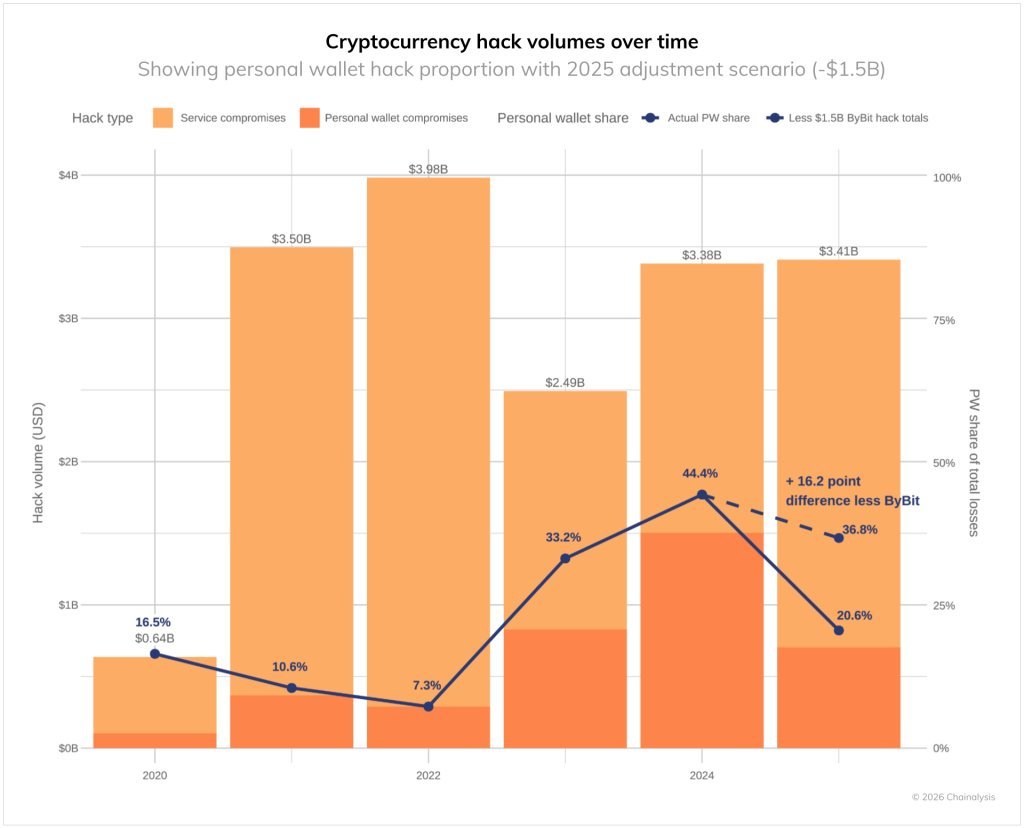
Annual losses linked to cryptocurrency theft have already reached $1.4 billion. This attack vector does not require breaking encryption, but rather compromising middleware that most users never examine.
Stand-alone YOLO sessions are the point of highest risk exposure. When an agent performs multi-step transactions without human checkpoints for confirmation, the malicious router has a wider operating window and the user has no leeway to detect anomalous behavior.
The founder of Solayer, known as @Fried_rice, highlighted these findings via Platform
26 LLM routers secretly inject malicious tool calls and steal credits. One of them emptied our client’s wallet of $500,000.
We also managed to poison the routers to pass traffic to us. In a few hours, we can directly support around 400 hosts.
Check out our article: pic.twitter.com/PlhmOYz2ec– Chaofan Shou (@Fried_rice) April 10, 2026
The defenses recommended by the researchers are based on the client side: closing errors that interrupt execution when abnormal responses are detected, filtering strange responses, and logging logs that cannot be manipulated by the router itself. Longer term, the UCLA team is calling for digital signature standards that make responses from large language models verifiable, the same architectural principle that makes Oracle’s integrity on the web a fundamental design requirement rather than an afterthought.
The post Warning: AI Infrastructure Attacks Drain Digital Currency Wallets appeared first on Cryptonews Arabic.