Not everything in Bitcoin is threatened by a quantum computer.
Bitcoin mining, the process by which new blocks are added to the blockchain, uses a type of mathematics called hashing that quantum computers cannot significantly break. The ledger itself and the rule that new bitcoins can only be created through mining would survive a quantum attacker. Blocks would still be produced and the chain would continue to run.
What will not survive is property.
Bitcoin wallets are protected by a different type of math that turns a secret private key into a public address that anyone can see. The math easily works one way and not at all the other, which is the only thing stopping a stranger from spending your coins.
The first part of this series on quantum computing focused on physics. A quantum computer is not a faster version of a classical computer. This is a fundamentally different type of machine, one that starts from a very small, very cold metal loop where the particles behave in a way that they don’t behave anywhere else on Earth.
Part two explained what happens when you point this machine at Bitcoin. Bitcoin wallets depend on a one-way math problem. Transforming a secret private key into a public address takes a few milliseconds. Going back the other way, from public address to private key, would take an ordinary computer longer than the age of the universe.
A quantum algorithm called Shor bridges this gap. Google’s paper published this month showed that the attack could be carried out with far fewer resources than previously estimated, in a window that rivals Bitcoin’s block times.
This piece, the last in the series, is about the answer. What the real risks are, what Bitcoin has done about it, and whether a network built to withstand coordinated changes can coordinate the largest security upgrade in its history before the hardware catches up.
What is exposed, what is safe
The risk pool is vast.
About 6.9 million bitcoins, or about a third of all that has been mined, are in wallets whose public keys are already permanently visible on-chain. The bulk is bitcoins from the network’s early years, stored in an address format that published the public key by default. This also includes any wallet from which spending has already been made, because spending reveals the key to what is left.
A quantum attacker would not need to race against a transaction in progress. Instead, they could go through wallets with keys already exposed at their own pace, one by one. Bitcoin’s pseudonymous creator, Satoshi Nakamoto, holds approximately 1 million bitcoins, untouched since the network’s inception, and that pile is now in the exposed category.
The Taproot 2021 upgrade has expanded the issue. Taproot is a change to how Bitcoin addresses work, intended to make transactions more efficient and private.
A side effect was that any bitcoin spent since Taproot was activated published the key protecting anything left at that address. This was not a mistake but a reasonable compromise at the time, when quantum delays seemed much longer than today.
What’s in the works?
While the quantum threat has sparked heated debate in recent months and other blockchains are gearing up, nothing concrete has yet emerged from Bitcoin developers.
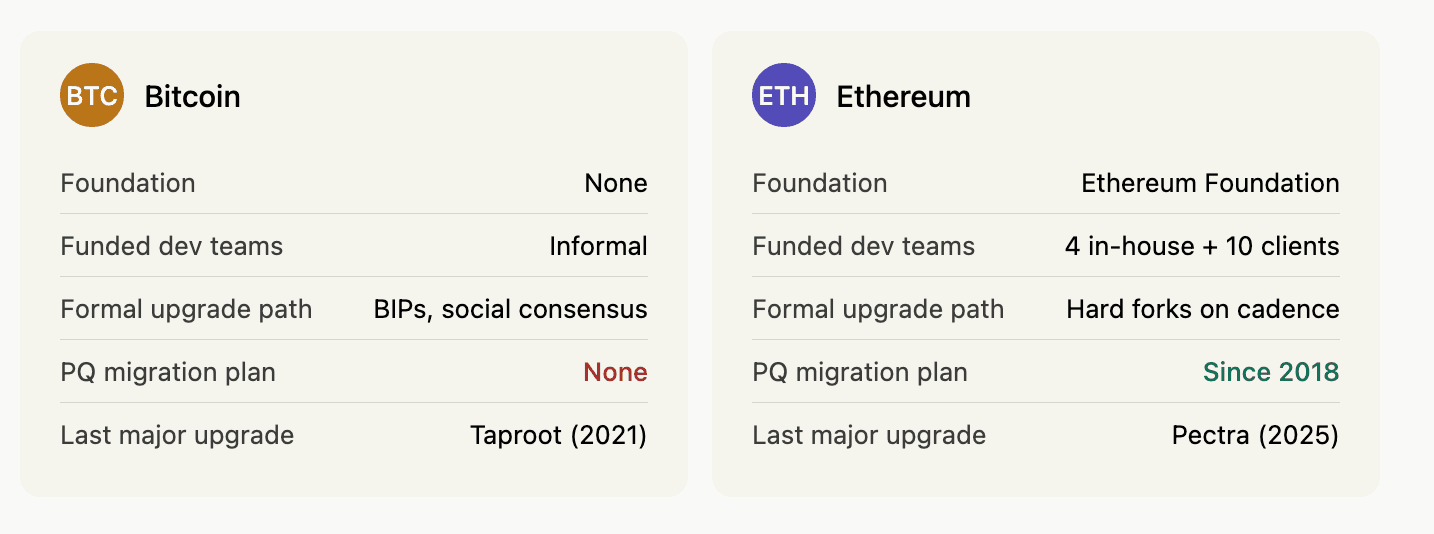
Ethereum, which can be considered one of Bitcoin’s biggest competitors among institutional investors interested in the crypto market, has had a formal quantum resistance program since 2018.
The Ethereum Foundation leads four teams working full-time on the migration, with over ten groups of independent developers shipping testnets weekly. The plan calls for specific upgrades for four upcoming network-wide changes, moving Ethereum’s security to new mathematics that quantum computers cannot break. He even launched a dedicated website, pq.ethereum.org, to publish his progress.
Bitcoin has no equivalent strategy so far.
This is not to say that there is no effort to resolve it.
One such formal proposal is BIP-360 from a group of developers and researchers. This would add new types of quantum-secure addresses that holders could voluntarily migrate to. A competing proposal from BitMEX Research would install a detection system that would trigger defensive action if a quantum attack is observed on the network.
However, neither has widespread support from Bitcoin’s core developers, and the two proposals solve different halves of the problem.
Nic Carter, one of Bitcoin’s prominent advocates, has denounced it in recent months.
“Elliptic curve cryptography is on the brink of obsolescence,” Carter wrote on X, referring to the mathematics that secures Bitcoin wallets. He described Ethereum’s approach as “best in class” and Bitcoin’s as “worst in class”, citing developers who are “denying, gaslighting, maintaining control, burying their heads in the sand” rather than tackling the problem.
Adam Back, CEO of Blockstream and one of Bitcoin’s early significant contributors, disagrees on the urgency but agrees on the direction.
“Quantum computing still has a lot to prove. Current systems are essentially laboratory experiments,” Back said at a conference earlier this month. But he also said Bitcoin should be prepared now, with optional upgrades built in advance so the network can migrate when needed, rather than rushing in a crisis.
The coordination problem
So what is the biggest challenge in implementing effective solutions against the quantum threat of Bitcoin?
Bitcoin migration is more difficult than Ethereum for reasons unrelated to actual mathematics.
Ethereum has a foundation that funds engineering work and a governance process that regularly adopts major upgrades. Bitcoin has neither. Its development culture views any central authority as a failure mode, and its social consensus holds that changes to protocol should be rare and difficult.
These priorities have allowed the network to remain stable for nearly two decades, but they also make the quantum structural problem more difficult for Bitcoin to solve.
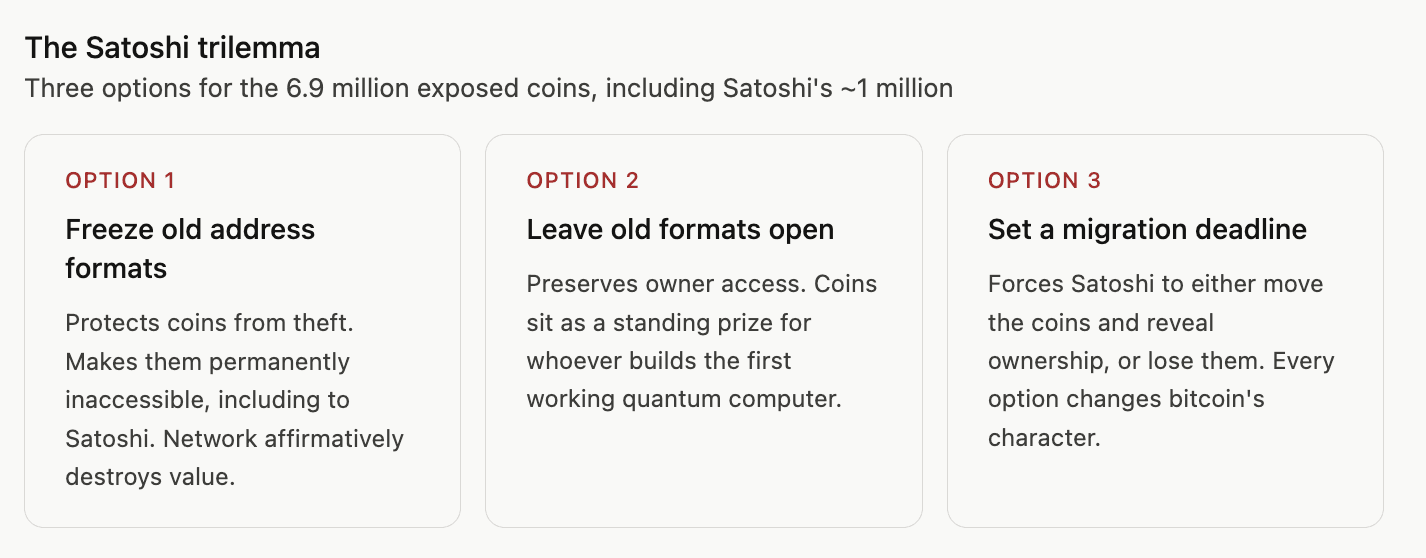
Migrating the 6.9 million exhibits requires decisions that the network has spent twenty years avoiding. Should old address formats be frozen after a certain date to protect coins from future theft? Should exposed coins be allowed to move to new quantum-secure addresses using their original keys? What happens to part owners who can’t or won’t migrate?
The Satoshi coins are the most striking example. Freezing old formats protects the pieces from theft but makes them permanently inaccessible, including to Satoshi. Leaving older formats open means these coins are a permanent prize for anyone who builds the first working quantum computer or has access to a quantum computer and wants to attack.
Setting a migration deadline forces Satoshi to either move the pieces, revealing their ownership, or lose them. Each option changes the character of bitcoin in ways that the network has apparently refused to change.
What happens next
Google’s own framing of the document is a summary of the industry’s situation.
A successful attack on the mathematical uses of bitcoin “should not be seen as a wake-up call for the adoption of post-quantum cryptography, but rather as a potential signal that PQC adoption has already failed.”
This means that by the time the threat becomes visible, the response window may have already closed.
Developers now face the question of whether a network built to withstand coordinated change can coordinate the largest security upgrade in its history before the hardware catches up with the theory.
Ethereum’s eight-year lead suggests the right answer is to start now. Bitcoin’s governance culture suggests that the likely response is to wait until the threat is demonstrated and then act.
Only one of these answers works if the delay turns out to be shorter than the optimists’ estimate.


