Kraken confirmed Monday that it was the subject of an extortion attempt by a criminal group possessing videos of its internal systems containing customer data, and the cryptocurrency exchange explicitly stated its refusal to comply with their demands.
Nick Percoco, the company’s chief security officer, revealed this threat via the X Platform on April 13, 2026, explaining that the company is currently working with federal law enforcement in multiple jurisdictions to pursue and arrest the perpetrators.
This rejection is the right decision and a calculated institutional signal at a time when trust in trading platforms is structurally fragile.
Most important key points:
- What was hacked: Access to internal systems containing customer data through insider recruitment; The system was not completely compromised and customer funds were not at risk, according to Kraken.
- Scope: The information of approximately 2,000 people was potentially accessed, representing approximately 0.02% of Kraken’s total user base; All affected users have been contacted.
- Blackmail mechanism: The criminals are threatening to release videos of Kraken’s internal systems and distribute part of customer data to media and social media platforms unless their demands are met.
- Kraken replied: Percoco publicly declared: “We will never pay these criminals; we will never negotiate with subversive actors,” and emphasized the active involvement of federal law enforcement.
- Internal distribution model: An incident in February 2025 involved a similar video shared on a criminal forum; In both cases, a person within the company was identified.
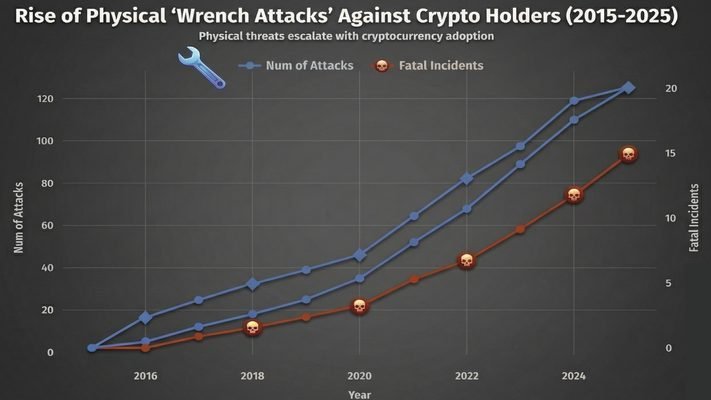
- Sector context: Keystroke attacks against crypto industry employees have increased by more than 75% annually, with CertiK attributing more than $40 million in confirmed losses to these attacks last year.
- What to watch out for: Will investigations lead to arrests and how the delay in Kraken’s IPO timeline will factor into the impact on its reputation after a second consecutive security incident.
How the Kraken Hack and Extortion Mechanisms Were Actually Implemented
This operation was not the result of a protocol vulnerability or credential theft. The entry point for the February 2025 incident and the current threat of blackmail was the recruitment of internal employees; Trained individuals within the Kraken organization were given access to internal systems, allowing for a reconnaissance operation rather than a complete hack.
Access appears to have been limited to read-only, which was sufficient to videotape customer data without triggering immediate exposure of the systems.
Percoco confirmed that Kraken received information about a video showing sensitive customer information of its internal cryptosystems, the same mechanism used in the February 2025 case, when a similar video appeared on a criminal forum.
Kraken Security Update
We are currently being extorted by a criminal group who are threatening to release videos of our internal systems showing customer data if we do not respond to their demands. It’s important to start with the most important points: our systems have never been…-Nick Percoco (@c7five) April 13, 2026
In both cases, an insider was identified as being involved. Criminals are now threatening to distribute these videos and associated customer data to local and social media outlets unless Kraken complies with unspecified demands. The exact financial amount required for the extortion operation has not been made public.
Percoco described this model as deliberate and evolving, saying: “We are working with industry partners and law enforcement to investigate and disrupt insider recruitment efforts targeting not only crypto companies, but also gaming and communications organizations.
This isn’t just an opportunistic hack, this is a coordinated recruiting infrastructure that operates on high-value data segments, and Kraken naming it this bluntly is indicative of how the industry as a whole will respond.
Reports indicate that emerging crypto theft vectors are increasingly targeting infrastructure access rather than exploiting network vulnerabilities, and employee recruitment fits into this threat profile.
What user data was exposed and what was the consequence?
Kraken has not publicly identified the categories of data captured in the videos, whether “know your customer” (KYC) documents, wallet addresses, transaction history, or account metadata.
But what has been confirmed is that around 2,000 people have had their information exposed, and Kraken said it has already contacted everyone in danger. Access was read-only and internal systems were not compromised in the full sense of a large-scale data breach.
The practical risk for affected users is not account takeover, where no funds are accessed, but rather targeted social engineering and physical exposure.
With names, addresses and account data in the hands of criminals, affected users become targets of the same physical attack vector tracked by TRM Labs, which resulted in more than $40 million in losses last year.
This figure is likely an underestimate, given the practice of underreporting such incidents. Kraken’s decision to contact affected users is the right thing to do; However, it has not yet been confirmed whether this communication included specific security guidelines, recommendations on the use of physical security keys, a change of address or increased vigilance.
The post Kraken Platform Refuses to Submit to Blackmail by Hackers Threatening to Leak Customer Data appeared first on Cryptonews Arabic.